Large corporations can afford to invest in expensive security measures to protect themselves against cybercrime, therefore small and mid-sized companies are becoming increasingly vulnerable to attack. As new security technologies are developed, cybercriminals are investing in more advanced strategies – mobile malware, ransomware and botnets – to access valuable data that many small and mediums organizations hold.
Network security is a critical part of health. Your organizations data and IT systems must be reliable, secure and protected. We work closely with you to determine exactly what you currently have and how to keep that protected from outside threats and follow any and all security and compliance regulations required for your organization.
In light of the rapidly evolving marketplace, business security must also adapt. We take a high-level approach to your business protection, providing a customized network security solution around your specific operations. From core perimeter protection to highly defined points of entry and end points, our multi-layered approach to network security is the offense and defense needed to help protect your organization in the rapidly changing world of technology.


Companies in a variety of industries may need to keep their network in compliance with a range of industry regulations. Companies processing credit card information need to maintain PCI Compliance, while healthcare professionals may need to maintain HIPAA Compliance. Sarbanes Oxley (SOX) compliance may be required for financial reporting.
Most businesses recognize the need to secure and protect applications and their data, including customer records, private employee data, competitive information, and trade secrets.
Depending on your industry regulations there may be strict requirements and steep fines for noncompliance. The risk of cyber attacks also increases the need to maintain a compliant network.



Offerings
Content Filtering
Employee access to dangerous or inappropriate website content can cause lost productivity and potentially introduce outside threats. Most the time however, the internet is an important asset to access. Web content filters is one way to protect your organization from such threats.
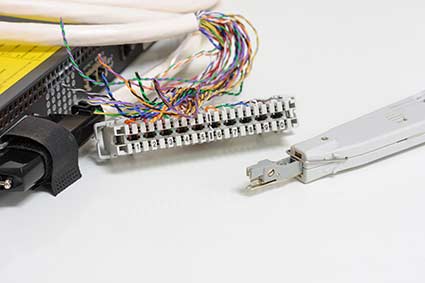
Security Appliances
Security appliances such as firewalls can protect against viruses, spam, spyware, intrusions and other threats. They also can allow you to prioritize mission critical applications with real-time visualization capabilities, so that bandwidth is being used for your organization to be as efficient as possible.
Virus and Malware Protection
We can assist to implement a proactive anti-virus and malware protection program to shield your network from threats of viruses, spyware, Trojans, malware and more.
Message Filtering
Many businesses can benefit from an e-mail/spam filters due to lost productivity caused by large amounts of email. Some organizations have compliance requirements which require end-to-end encrypted communications system. We can provide you with a custom solution for your needs.
Message Encryption
Some organizations have compliance requirements which require end-to-end encrypted communications system. We can provide you with a custom solution for your needs.
Security Best Practices
We can assist with IT Process Control and Management, IT Process Guidance, and IT Risk Management based on ITIL, ISO 17799, ISO 15408 or ISACA/ITGI Harmonization Document.
Identity and Access Management
Identity and access management (IAM) can be a framework for organizational processes that can control user access to critical information within their organization. Identity and access management products offer role-based access control, which regulate access to systems or networks based on the roles of individual users within the organization.
Two Factor Authentication
Two Factor Authentication is an extra layer of security that is known as “multi factor authentication" that requires not only a password and username but also something that only, and only, that user has on them, such as a physical or digital token.
IP Surveillance
Surveillance cameras are an excellent way to both prevent and reduce theft. The mere presence of a security camera is sometimes enough for a prospective thief to rethink their plan of action. With a surveillance system in place, incidents of theft can be reduced dramatically, saving your business money and keeping your store and offices secure.
Training
We can provide the critical link between people, processes, and technologies that make a security program work by providing the training your employees need to maintain the integrity and security of organizational data to ensure you maintain compliance.
What are SIP Trunks?
As a business owner, you are constantly looking for ways to cut costs and re-prioritize your spending. With all the services you are tasked with managing (merchant services, shipping services, payroll services, etc.) it’s understandable you haven’t mastered the knowledge of each industry. Maybe you’ve heard of SIP trunking, and…

Device configurations need to be backed up as well
Device configurations need to be backed up often to maintain a repository of backups ready to be restored in case of emergencies. In large enterprises with more number of devices, this task of getting the device configuration backup up becomes a huge mundane task taking up most of the time…

Secure Offsite server backup software provides more than piece of mind
Data is the most important aspect of your computer. An operating system can be reinstalled and so can applications, but it may be difficult or impossible to recreate your original data. It is essential that you always back up your important information and have a plan for recovering from a…
